Defense and Military Organizations
Win the war on cybercrime with impenetrable, trusted security
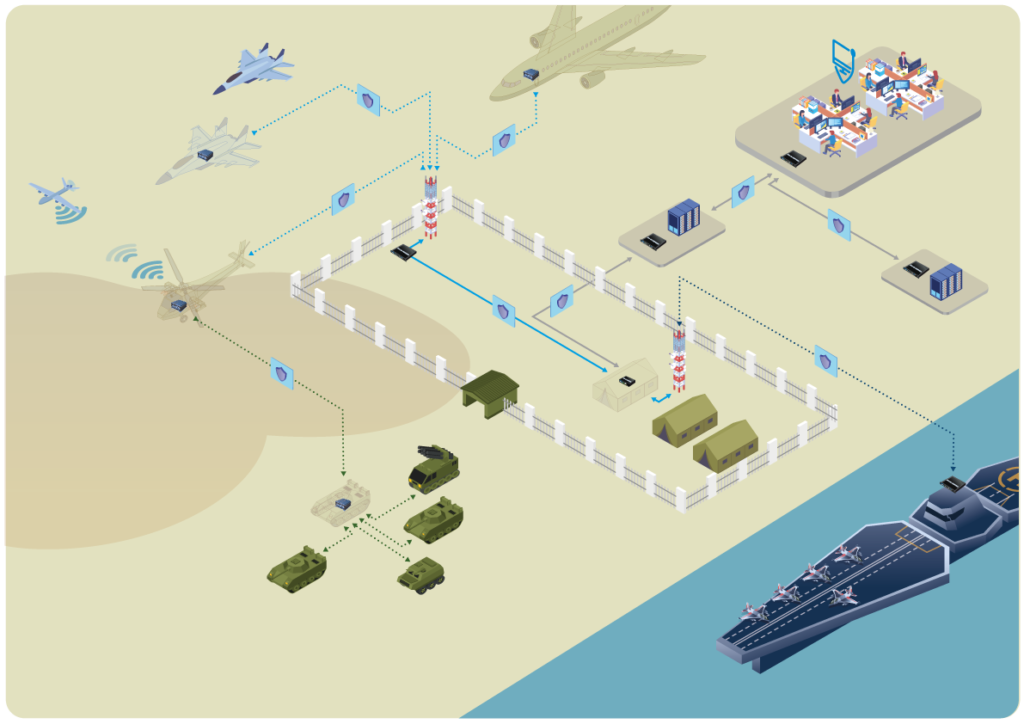
Military organizations, defense ministries, and armed forces need especially powerful protection for their information systems. In the modern era, cyberwarfare plays a crucial role in national security – and the best offense is an unshakeable defense. Security, reliability and availability are therefore of the utmost importance when the stakes are so high.
Security solutions for the defense sector require quality guarantees. The standards and certifications offered by independent organizations ensure that trusted solutions have been certified by a third party.
Our solutions are NATO and EU Restricted certified for protecting sensitive information. These certifications guarantee that quality and security are crucial priorities in product development. As a sign of trustworthiness, all Stormshield products have obtained ANSSI’s standard qualification and their encryption is guaranteed. Most of the security components of Stormshield products are also EAL3+ certified, and the network filtering components are EAL4+ certified.
Further, as a Defense and Military organization, the confidentiality of your operations is critical to national security. This need for privacy applies not only to cyber criminals, but also to other State actors such as intelligence agencies. Our promise to you: no backdoors for anyone, for any reason.
All these certifications demonstrate that Stormshield solutions continuously remain at the cutting edge of emerging security needs. In addition, they are recognized as trusted products by all of the European countries that have ratified the Mutual Recognition Agreement. These certifications provide assurance that our products are properly designed, tested, and implemented according to governmental requirements. This unique level of certification guarantees that you are opting for uncompromised, high-performance security only offered by a leader in the cybersecurity market.
Losing confidential data or information is not an option in the defense sector and military organizations. Applications and communications, especially confidential communications, are protected through strong, vital encryption.
The intrusion prevention system (IPS) in Stormshield Network Security products combine behavioral and protocol analysis to ensure effective, proactive protection against attacks, especially zero-day attacks. Our EAL3+ and EAL4+ certified technology is among the most powerful on the market and was designed to guarantee the highest level of security and performance.
Switch to a better workstation protection technology with Stormshield Endpoint Security behavioral analysis. Working within the operating system, our tool intercepts and analyses all commands in order to detect unusual behavior that might exploit flaws in applications. Since it does not use a signature database, it is particularly effective for non-connected environments. Stormshield Endpoint Security provides smart protection against both known and unknown attacks, regardless of their level of sophistication.
Encrypting sensitive information at its source helps prevent confidential data from leaking or being stolen. This EAL3+ certified product guarantees a level of encryption that meets the strictest standards. Its end user-centered approach makes it easy to use, thus limiting the potential to bypass the security system. Stormshield Data Security’s certified encryption solution is compatible with all third party applications so as to facilitate integrating the encryption of your data into your business applications.
SNxr1200: an encryption firewall adapted to heavy constraints
Discover our network security product, designed to be embedded in vehicles operating in critical environments for extreme aeronautical, space and military missions.

Because military organisations, ministries of defence and armed forces require particularly strong protection for their information systems, all these organisations must comply with a number of cyber rules and standards. In addition to the national level, these organisations must comply with European cybersecurity regulations such as the RGPD, the Cybersecurity Act or the NATO Restricted Classification. Other standards (e.g. Common Criteria EAL3+ & EAL4+ or ISO/IEC 27000 series) are not mandatory under current legislation but help to improve the level of cyber security of defence organisations.
Stormshield products help organisations comply with these requirements by improving the cyber resilience of their infrastructure. For example, Stormshield Network Security and Stormshield Data Security have been awarded NATO Restricted Distribution. These solutions can therefore be deployed in sensitive environments to encrypt information classified as NATO Restricted, and to enable secure transmission of classified information. For more information on Stormshield's compliance with Defence cyber regulations, please see our dedicated document.
Implementing a security product in an existing environment can be a tedious process: the product must be flexible and have an adaptable network layer so that it can fit into your architecture without causing downtime. Our solution is adjustable and integrates seamlessly into your existing infrastructure to ensure you spend more time on what matters to your organization.
Whether in routed, transparent, or hybrid mode, you choose how you want to use our equipment. The network layer can be adjusted for integration with any complex architecture. Built-in routing features adapt easily to other previously installed equipment as well.
The growing need for multiple network security solutions and equipment can greatly complicate administrative tasks. Our centralized administration solution simplifies the management of your entire IT system and the delegating of rights for borderline cases.
Centralized management helps limit the time you spend managing remote equipment by giving you a single console. It also enables you to efficiently manage all of your Stormshield products.
Setting up encrypted networks is often required for an optimal exchange of secure information. Do you need mobility or site-to-site connections? Based on technology that is certified at the highest level, the IPSec VPN and SSL VPN modules provide you with complete protection thanks to unbreakable encryption of data flowing through secure tunnels.
Whether your certification authority is internal or external, our PKI certificate management module ensures that digital certificate enrollment and tracking is a simple, centralized process. With this module, you get to take advantage of high-performance authentication and comprehensive management of user rights.
Do you have specific requirements regarding your organization’s security constraints , such as securing configuration exchanges? Stormshield offers sensitive markets specific services to: