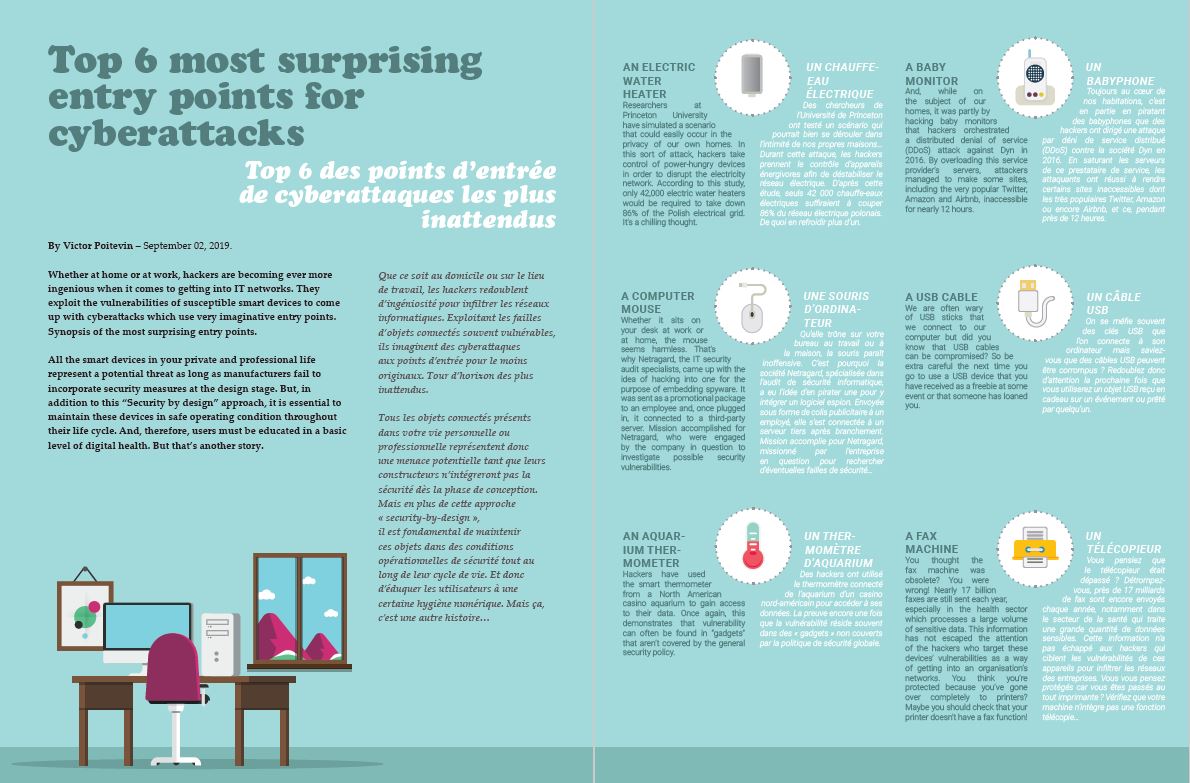
Top 6 most surprising entry points for cyberattacks
Whether at home or at work, hackers are becoming ever more ingenious when it comes to getting into IT networks. They exploit the vulnerabilities of susceptible smart devices to come up with cyberattacks which use very imaginative entry points. Synopsis of the most surprising entry points in this infographic.