
As part of the digital transformation process, the increasing openness towards the outside world and the interconnection of different information systems make companies more vulnerable to cyber-attacks. However, there are effective ways of protecting oneself, such as the segmentation of the information system. A technique that makes it possible to contain threats by preventing them from spreading to other areas. This also optimises the performance of the equipment. But how can the network be segmented? And in the age of Industry 4.0, when we consider operational requirements, business continuity and obsolete systems, is it really that simple in the industrial world? We propose some answers.
Network efficiency and security
Network segmentation is initially very important for purely functional reasons: to guarantee the availability and efficiency of equipment. When too many items of equipment are connected to the same network, with innumerable communication flows and private connections, a sort of “background noise” is generated. In an industrial environment, for example, the PLC will not be able to ignore it: even if it does not process all requests, it analyses them systematically. This runs counter to the requirement for operational efficiency in this area of activity. “This background noise diverts the PLC from its primary function, a situation that can quickly lead it to reach saturation and therefore to malfunction. A factory cannot continually expand its network architecture without segmenting it”, explains Vincent Riondet, Delivery Manager at Schneider Electric.
But it is regarding cybersecurity that segmentation brings its greatest benefits. Segmenting areas according to each person’s specific usage requirements allows us to provide employees with only the resources and access they need. The data related to organisational, operational and automatic systems is thus contained in zones which may themselves contain sub-zones. Segmented in this way, they are less likely to leak or be compromised. “In order to achieve this division into homogeneous networks, it is necessary to carry out a precise inventory of your equipment and its types, and to know how the items of equipment are physically connected to each other. All this information will allow us to access a communication matrix and launch a risk analysis: this is essential to know what to prioritise and how to segment everything”, adds Vincent Riondet.
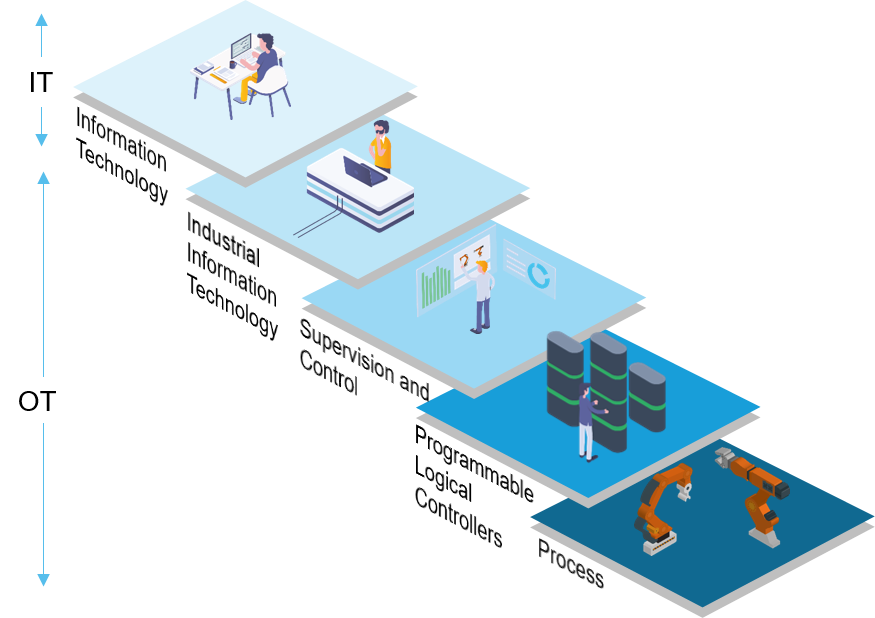
IT/OT: multiple levels of segmentation
In the beginning, there was IT. Within companies’ information systems, initial levels of segmentation are needed to separate certain groups of services or computers, according to their exposure to cyber threats - mainly related to Internet connections. In the largest companies, there will therefore be a tendency to plan internal segmentation to isolate the departments exposed to the Internet, staff computers, internal services, but also field-based staff and visitors.
At the same time, under the influence of the digital transformation of companies and the advent of Industry 4.0, industrial networks have evolved over time under the dogma of IT/OT convergence. “Initially the industrial network was not connected to the IT system”, explains Tarik Zeroual, Stormshield Global Account Manager. “Today though, for governance and business reasons there is a real willingness on the part of companies to automatically collect information from the field. Operational and maintenance data is no longer enough. Industrial companies now want to know how often their equipment is used, as well as having information related to the breakdowns and downtime of this equipment”. Establishing a barrier between the worlds of IT and OT is therefore a fundamental security measure, in order to guarantee the cyber-protection of industrial networks.
This convergence represents a major challenge for most manufacturers, says Vincent Riondet. “The vast majority of our industrial networks are very poorly structured. They were installed and set up by automation specialists, so this is not their core business: they did not take into account the problems of IP addressing, broadcasting and flow management, for example. Their only objective was to make the items of equipment communicate with each other”. A challenge that is all the greater since the threat does not necessarily come from very far away. Factory employees and outside personnel still often use USB sticks, whether to collect data from the supervision workstation or to update PLCs. However, it is still common for them to become infected. A simple connection could corrupt an entire information system. “This segmentation makes it possible to protect against all internal and external threats, whether they come from the Internet or from external parties”, says Vincent Nicaise, Industrial Partnership and Ecosystem Manager at Stormshield.
Segmentation: more than just a recommendation?
Network segmentation is therefore the most effective measure to contain cyber threats and prevent malware from spreading within an IT or operational infrastructure.
It is also one of the key recommendations of the IEC 62443 standard. This industrial cybersecurity standard has developed the concept of division into “zones” and “conduits” according to the criticality levels of the dedicated equipment. A defence-in-depth logic which, thanks to the integration of firewalls, strictly and immutably determines the authorised and unauthorised communication flows between predetermined segments or blocks. Divided into blocks, the network as a whole becomes more difficult to attack by a cyber-criminal.
Recommended by the texts of the IEC 62443 standard, segmentation provides an essential bulwark to limit intrusions and deal with cyber-attacks. Like wearing a seatbelt in the car, this technique is a must - regardless of the type of network involved.
Physical or virtual separation
There are two segmentation methods: physical segmentation and virtual segmentation. Physical segmentation consists of creating parallel networks so that they are completely separate. A switch will be installed on each category of machine - PLC, PC, printer, etc. Virtual segmentation, on the other hand, offers the same hardware switch for the different items of equipment: connected to different ports on the switch, the latter are separated virtually by virtual networks (VLANs) simulating separate switches, thus making it possible to segment a physical network using software. They cannot communicate with each other unless they are linked to a firewall that allows them to do so.
“Both methods have proved their worth in terms of segmentation, one is no more vulnerable than the other in cyber matters, if they are done well. The only difference, in my opinion, is in terms of cost. Physical segmentation makes it necessary to purchase numerous new devices. Very few companies can afford this luxury. Virtual segmentation is the most economically viable”, says Tarik Zeroual.
NAT, a useful mechanism
In some cases, the implementation of network segmentation, whether virtual or physical, requires a change in the organisation of the addresses used by the items of equipment to communicate with each other. The factories initially deployed equipment according to operational needs, without taking into account the allocation of IP addresses. As the network was “flat”, all the items of equipment were able to communicate with each other without any problem. “But with zone segmentation, items of equipment can only communicate with those in the same zone, the same sub-network. However, it’s impossible to ask a factory that has spent fifteen years or so developing its industrial systems to reconfigure this equipment item by item and test it all over again to see if it all works. It would be a financial drain on them”, says Vincent Riondet.
To solve the problem in the short term, it’s possible to use the NAT (Network Address Translation) function. This system allows addresses to be “transformed”, to match IP addresses to other IP addresses. “This function involves translating an address in one sub-network to an address in another sub-network to ensure interconnection. It allows you to leave the applications untouched and not have to configure them again. NAT can be a temporary solution that allows information to pass through while waiting for industrial systems to be modernised or replaced”, continues Vincent Riondet. “We have clients with whom this migration scenario is spread over two years. However, we have already laid the foundations for these future reconfigurations, set our targets and defined our segmentation strategy. But in the background, it takes time on every maintenance stoppage. The industrial sector is complex, and we have to move forward step by step. Without NAT, most industries would not be able to secure their systems”. Address translation also makes it possible to integrate an industrial subsystem into the overall operational infrastructure without losing the manufacturer’s or service provider’s certification.
And so, as we have seen, the segmentation of the information system is a complex operation that takes time. To achieve defence-in-depth, it’s therefore vital to get down to work on it without further delay!
