Introduction
In a context of rapidly increasing cyberattacks, cybercriminals are constantly developing new techniques to trap users. Among those recently industrialized, the ClickFix technique has seen strong growth since it was first detected in March 2024.
It relies on social engineering to exploit users’ trust and persuade them to execute a malicious command on their own machine. It has become one of the most effective and widespread attack methods today, according to a 2025 Microsoft report (see page 36) indicating that 47% of initial accesses originate from the ClickFix technique.
What is the ClickFix technique?
The ClickFix technique is a two-step social engineering method where cybercriminals first simulate a crash or failure, then offer a reassuring solution that tricks the user into executing a malicious command on their own machine.
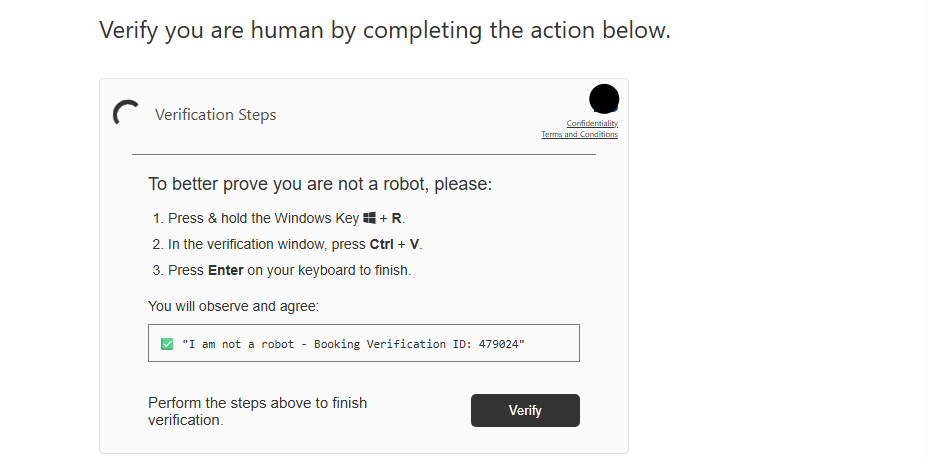
The principle: a compromised site or dedicated phishing page displays a fake security alert (anti-bot CAPTCHA, browser error, Cloudflare block, etc.) and shows a message guiding the user, for example:
To fix the problem, please do the following:
- Press Windows + R
- In the window that opens, press Ctrl + V (the malicious command having been copied directly to the clipboard by JavaScript code running in the background)
- Press Enter
Or also:
To fix the problem, please do the following:
- Click the "copy" button above
- Press Windows + X
- Open the terminal as administrator
- In the window that opens, press Ctrl + V then Enter.
The user thinks they are fixing a technical problem, but in reality, they are launching the first link in the attack chain (malware download, execution, or any other malicious action).
The illustration below shows a concrete example, with the identity of a well-known hotel booking brand being impersonated:
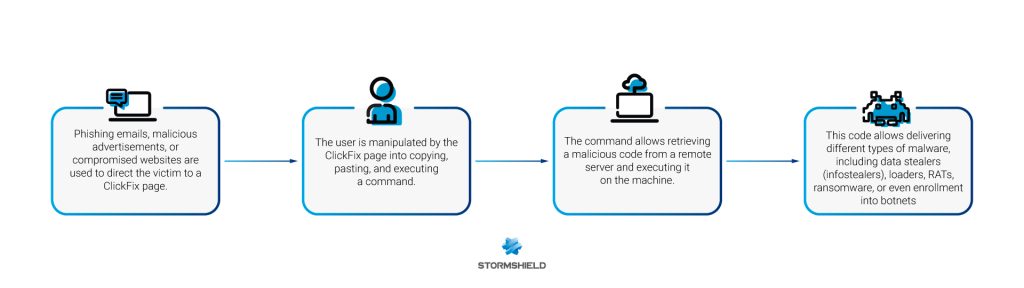
The diagram below shows the complete process of a ClickFix attack, from the initial click on the malicious site to the deployment of the malware.
Why is this technique effective?
The ClickFix technique exploits human psychology with:
- A feeling of frustration in the face of a malfunction (cognitive bias related to the fear of not being able to recover what the user came to seek).
- The legitimate appearance of known systems (Cloudflare CAPTCHA, browser verification...).
- Fake technical error messages that appear familiar (A feeling that the user understands the ‘problem,’ without raising their suspicion).
- Ultra-simple instructions (a few keystrokes and mouse clicks: minimal effort required to resolve the "problem").
- A lack of knowledge of the tools and commands used (the user executes without understanding the actual scope of the requested actions).
The user becomes an actor and executes the threat themselves, thereby bypassing traditional technical protections through manual and often obfuscated execution (long blank space hiding the true malicious command):
- Browsers: isolation/sandbox mechanisms, dynamic content analysis (scripts...), URL blocklists, tools like Safe Browsing
- Antivirus: static detection (file signatures)
- EDR (Endpoint Detection and Response): analysis of HTTP/HTTPS downloads, monitoring of launched processes
This approach frequently relies on the use of LOLBAS (Living Off The Land Binaries and Scripts): legitimate tools already present on the system (like PowerShell) that are hijacked for malicious purposes, making detection more difficult.
A rapidly growing technique
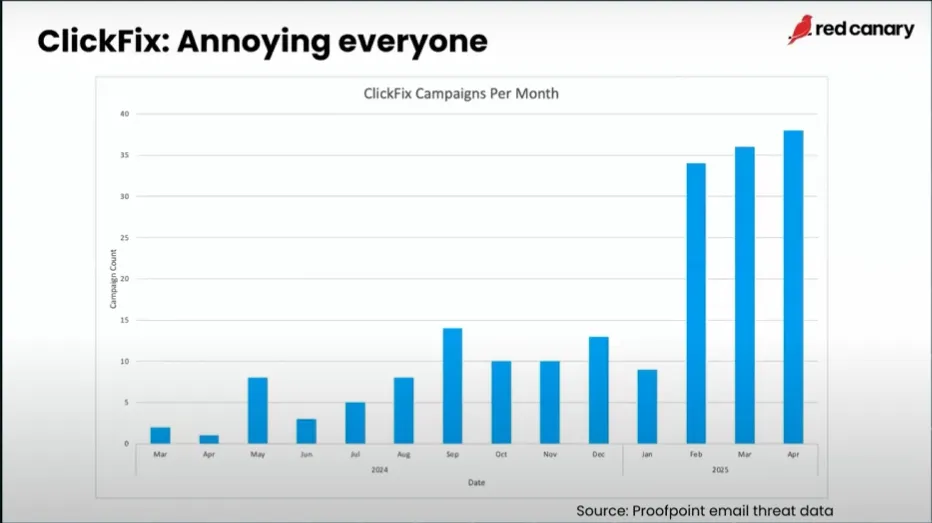
Since its first observation in March 2024, cybersecurity experts have observed a very rapid increase in ClickFix attacks. ESET reports a 500% rise in detections between late 2024 and mid-2025.
According to the MITRE ATT&CK classification, ClickFix falls under the Execution tactic, technique T1204 - User Execution, and more specifically the sub-technique T1204.004 - Malicious Copy and Paste.
This technique, now observed on different operating systems (Windows, macOS, Linux), is used by a wide variety of malicious actors:
- Independent cybercriminals
- Groups specialized in data theft (infostealers)
- State actors
It has also become a significant infection vector for malware campaigns such as Latrodectus, Lumma Stealer, and NetSupport RAT.
Here are the 2024/2025 figures according to Proofpoint:
Conclusion
The ClickFix technique illustrates the effectiveness of social engineering cyberattacks: by exploiting user trust, cybercriminals encourage them to deploy malware themselves. This bypasses the available security tools.
Cybercriminals continuously refine this technique to make it more persuasive. The main evolution of the technique relies on the emergence of variants like FileFix, which simulates the Windows Explorer instead of the "Run" dialog box, enticing the user to open a malicious file via a familiar interface.
User vigilance and security awareness remain the best defense, particularly against suspicious instructions such as opening Win + R.
In a forthcoming post, the Cyber Threat Intelligence team at Stormshield will present a detailed analysis of a ClickFix attack chain, including the study of malicious payloads and the technical steps of the attack.